OKTA (Classic) Authenticator Integration
This guide walks you through the process of setting up an OIDC-based Authenticator for Incode Workforce within your Okta environment.
Set up Guide
Step 1: Setup OIDC Identity Provider (IDP)
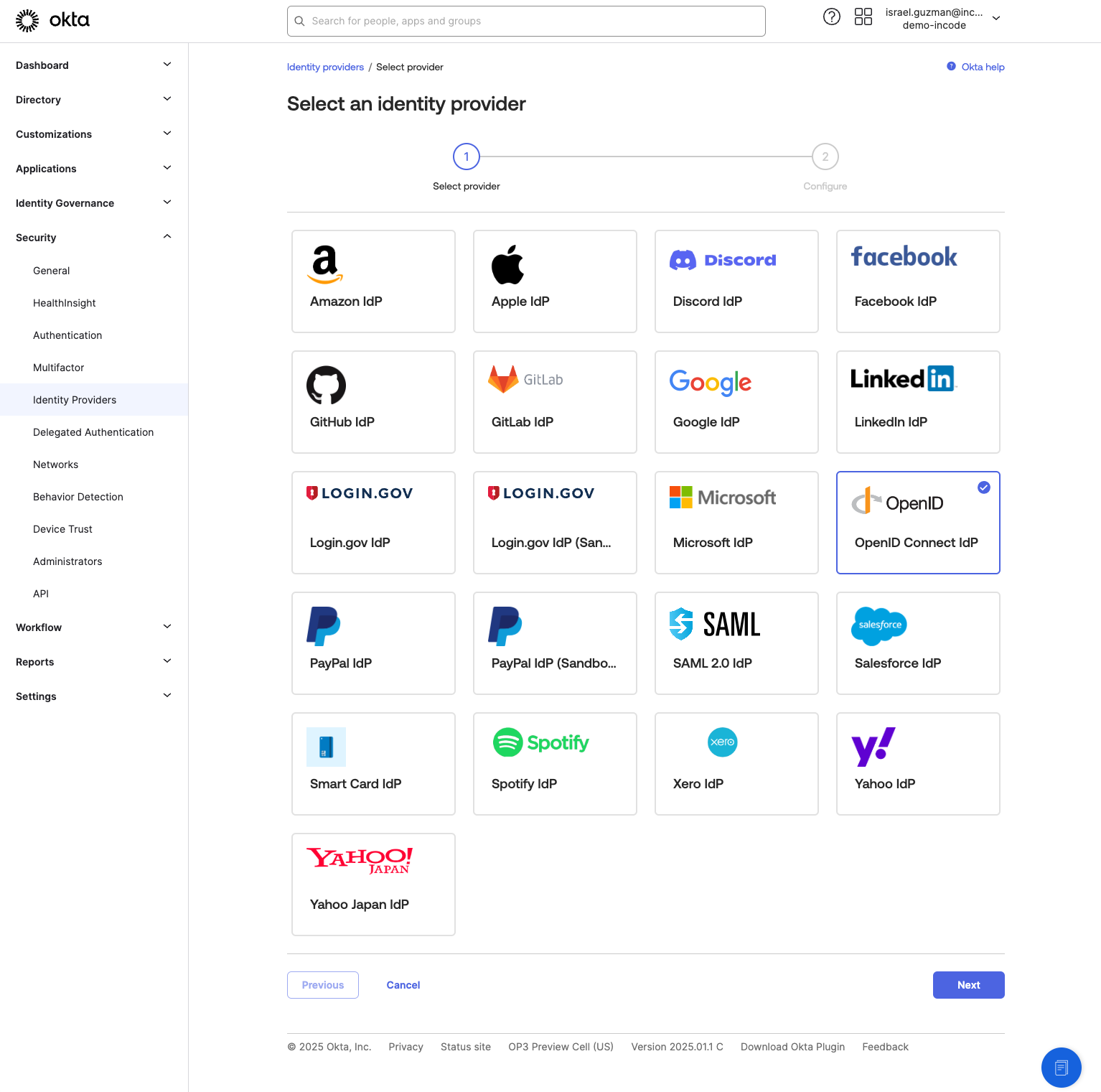
- OKTA Admin Dashboard Add Identity Provider: In the Okta Admin Dashboard, navigate to: Security -> Identity Providers -> Add Identity Provider, select the OpenID Connect IDP
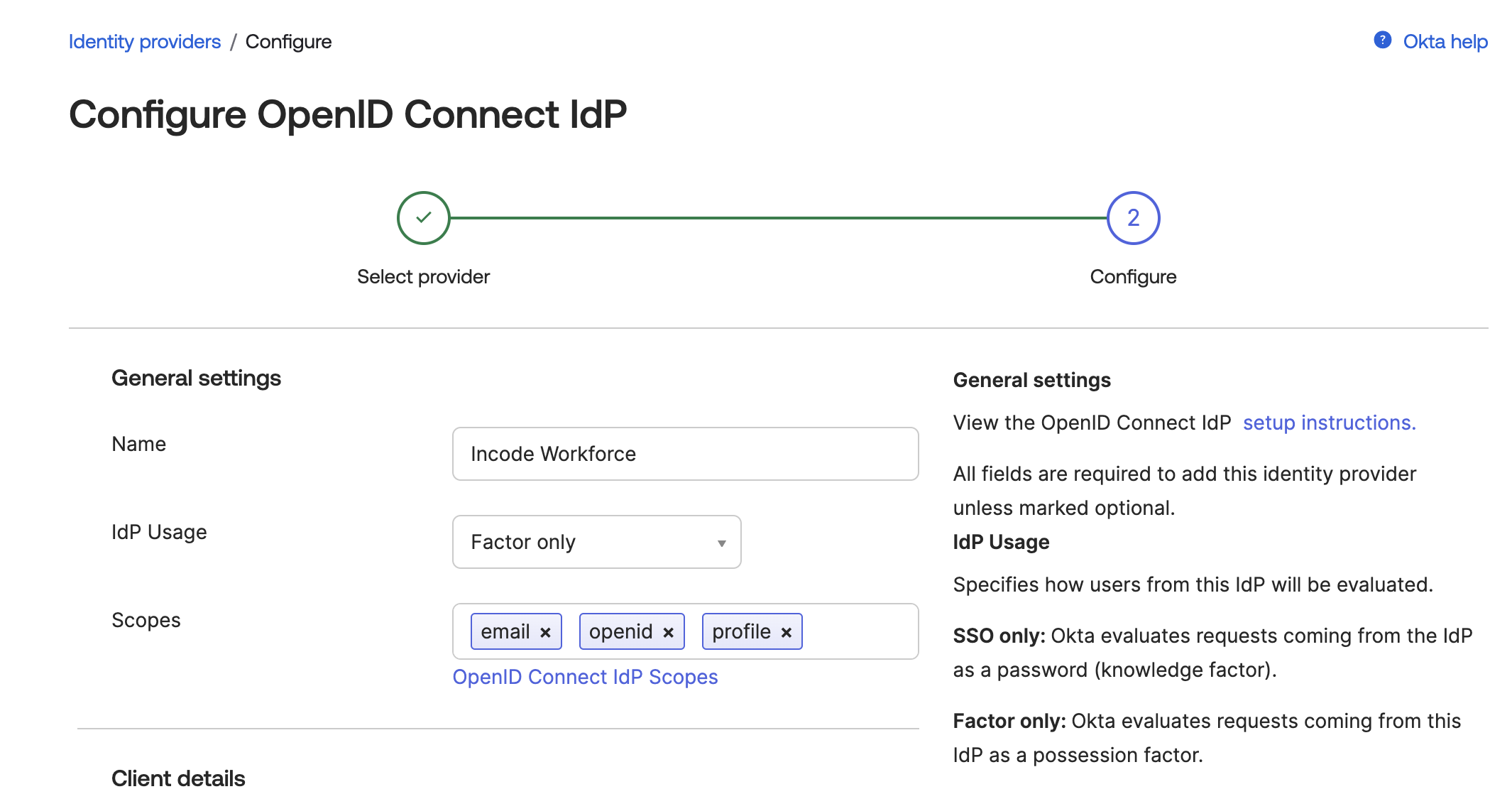
- OKTA Admin Dashboard Configure IDP: Add a name for IDP and change the mode to Factor Only. Make sure the scopes match the required scopes listed: email, openid, profile
- Workforce Dashboard Create OKTA Integration: In your Workforce dashboard, navigate to Integrations and click New Integration. Choose OKTA integration and click Continue.
- Workforce Dashboard Configure Integration: Give your integration a name. This name will be shown in analytics and give insights about verifications done with this particular integration.
- Workforce Dashboard/OKTA Admin Dashboard Copy Fields: Copy the following seven fields from the Incode Workforce Dashboard to Okta:
-
Client ID - Copy the unique client id generated for your integration to OKTA Client ID
-
Client Secret - Copy pre-generated Client Secret (or generate new) to OKTA Client Secret
-
Endpoints: - Copy corresponding endpoints to OKTA endpoints
- Issuer URL
- Authorize URL
- Token URL
- JWKS URL
- Userinfo URL
-
Copy these values to the corresponding OKTA Client ID, Client Secret, and Endpoints
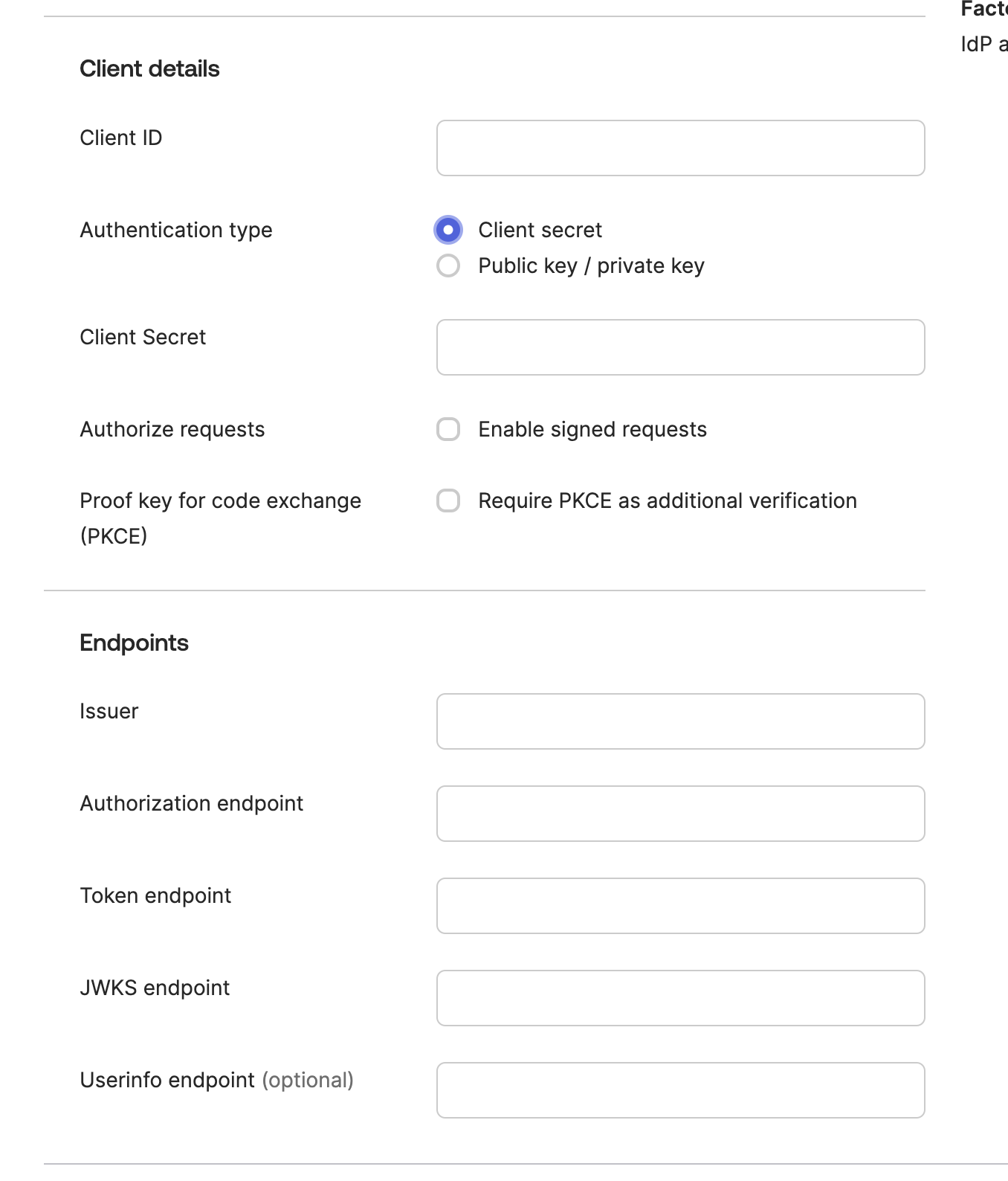
Fill out Client ID, Client Secret, and Endpoints with data from Workforce
- OKTA Admin Dashboard Save and Finalize: Choose Authentication type Client secret. After saving the IDP, return to the Incode Workforce Dashboard and copy the Redirect URI.
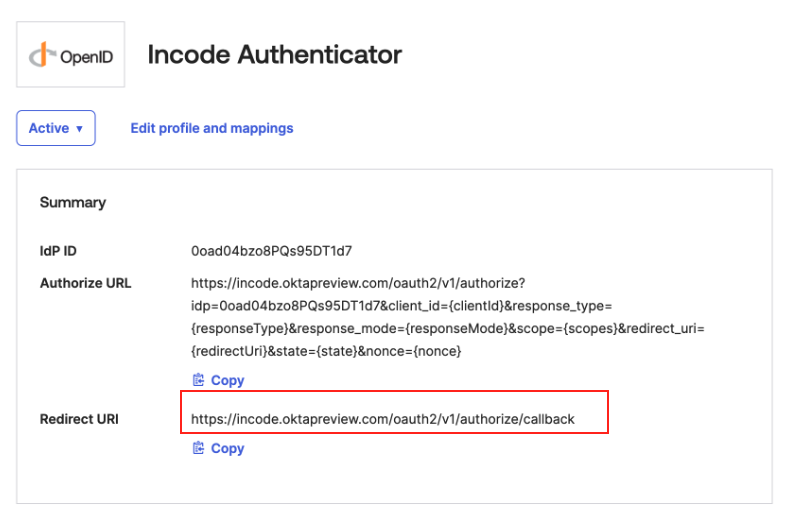
Copy Redirect URI
-
Workforce Dashboard Paste Redirect URI: In your Workforce Okta Integration go Back to and paste Redirect URI from OKTA to Redirect URIs.
-
Workforce Dashboard Review and Save: Review your settings by cliecking continue to move through steps. On last step click Save.
Step 2: Setup Authenticator that uses IDP setup in step 1
Once IDP is created, next step is to add an Authenticator within Okta that uses this IDP.
- Navigate to Multifactor: In Security -> IdP Factor, click on edit, and select in the Identity Provider (IdP), the name of the authenticator you want to use for authentication, and set it as active.
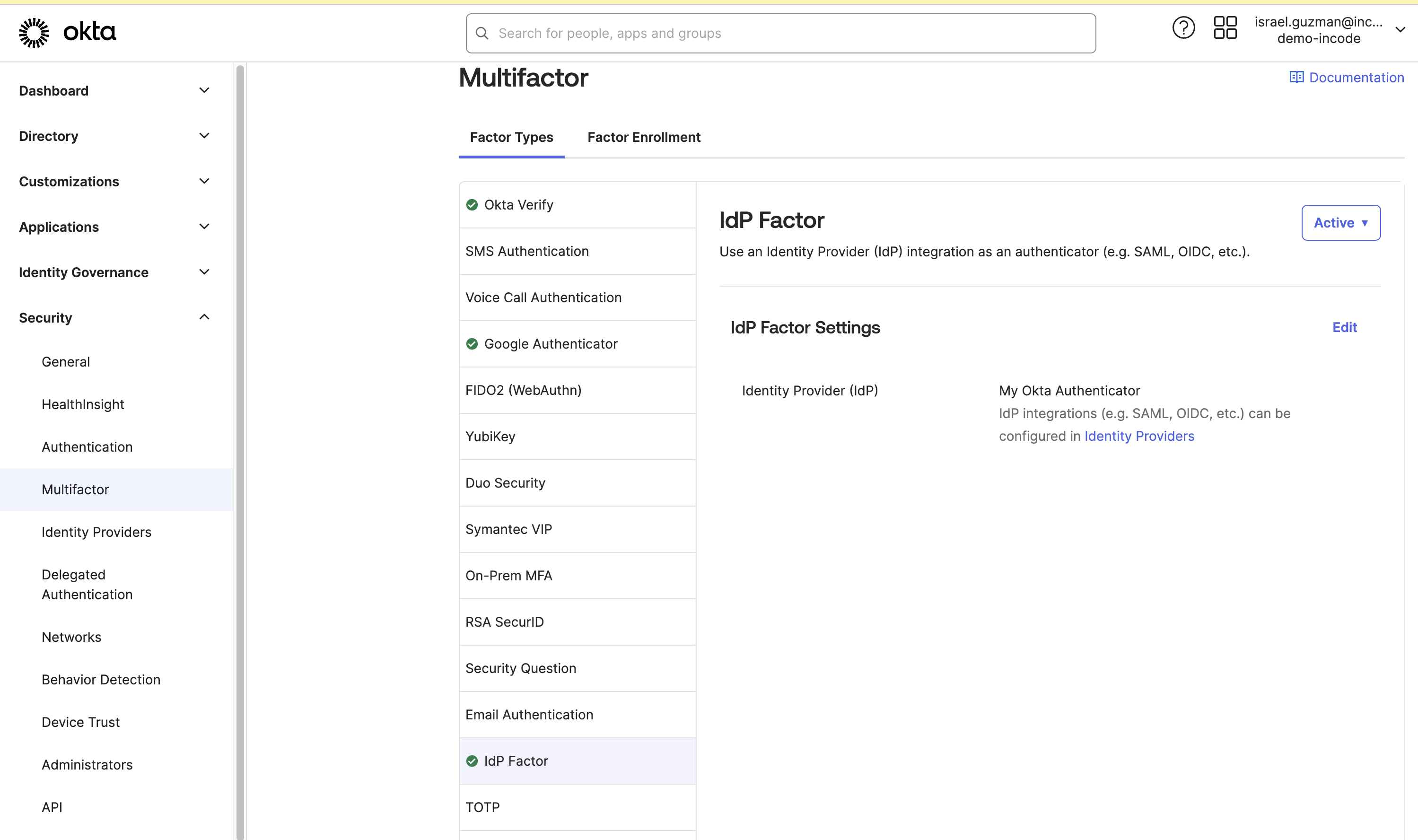
Note: If you don't see the IdP Factor, open a new ticket here to request Okta enable the feature flag "IdP Factor" and add the option to the Multifactor section for Your tenant.
Step 3: Create an Enrollment Policy for the Workforce Assigned User Group
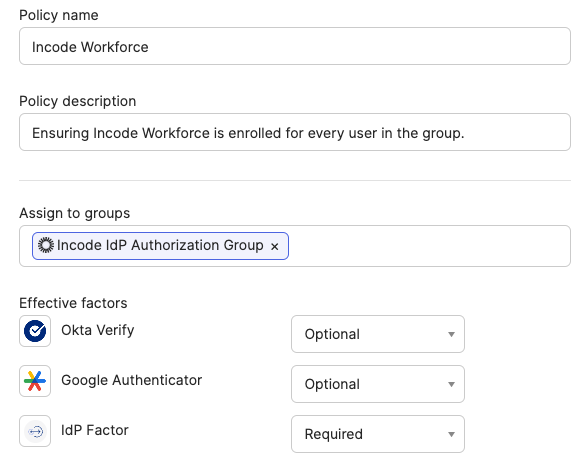
To ensure that every active Okta account in the assigned user group completes enrollment with the Workforce Authenticator, follow these steps. Okta checks for fulfillment of enrollment policies at account creation and every login so this ensures continued compliance, Go to Security / Multifactor
- In the Factor Enrollment (Tab) press Add Multifactor Policy:.
- Configure the Policy:
- Add a name and description for the policy.
- Assign to the group created for Workforce related to this policy
- Ensure IdP Factor is marked as Required, along with any other MFA methods your organization uses
Step 4: Add Rules as needed to use Workforce Authenticator during login
The Workforce Authenticator can be added as the highest assurance MFA method in your authentication policies:
- Navigate to Security / Multifactor to add rules In the Factor Enrollment (Tab)
- Press Add rule, assign the name for the rule, and customize it.
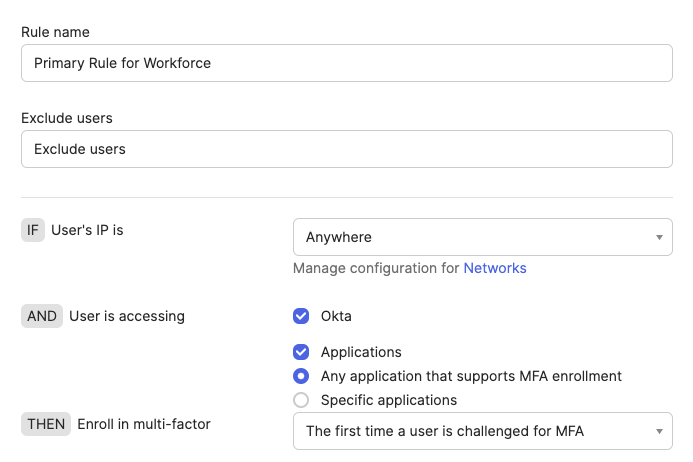
Okta adds new IDP authenticator as optional to default policy, make sure this is disabled if it is unwanted for your organization
Step 5: Test the Authentication Policy
Incode recommends testing the login process for the selected applications to ensure the new authentication policy works as expected.
Updated 7 months ago
